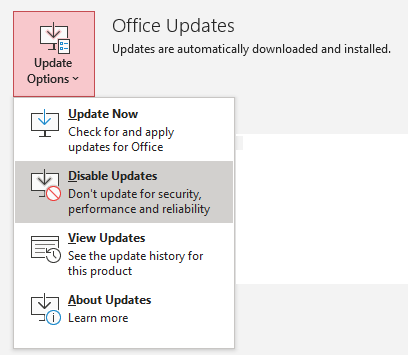
Microsoft released a new perpetual license version of Office 2024 which succeeds Office 2021. For more information on the release, visit Microsoft Office/Access 2024 Released.
Office 2024 can be installed on a PC directly from the Microsoft website. Enter your license and it’s automatically downloaded and installed.
Need the Office 2024 Setup Program
Direct, online installation works if you have an Internet connection and you’re the user. But that may not be the case when configuring a PC or VM with software that someone else runs in the future or in disconnected environments. It’s also helpful when consistency is desired to install the same software over time rather than whatever current download is available.
For these situations, it’s best to download the setup programs that can be used over and over. But where are the Office 2024 setup files?
Download the Office Deployment Tool
Microsoft doesn’t offer a simple download of an ISO setup file for Office. The Office Deployment Tool (ODT) is required to download the Office 2024 setup files. It is a free, small download here.
Once you download it, run it to extract the files into a folder you specify. It includes a setup.exe and configuration-Office365-x64.xml file that you need to edit for the download. The ODT (setup.exe) performs the instructions in the XML file.
Copy and Edit the XML File
Copy the configuration-Office365-x64.xml file to a new name to edit it. For instance, use configuration2024-64.xml for the 64-bit download specifications. You can use Notepad or an XML editor to edit it.
By default, the settings are for the 64-bit version of Office 365 which are specified this way:
<Add OfficeClientEdition="64" Channel="Current"> <Product ID="O365ProPlusRetail">
To get Office 2024 instead of Office365, change it to:
<Add OfficeClientEdition="64" Channel="PerpetualVL2024" SourcePath="C:\Office2024\64\"> <Product ID="ProPlus2024Volume">
The changes are:
- Channel to PerpetualVL2024
- Source Path is the folder where the files are downloaded to
- Product ID to ProPlus2024Volume
To get the 32-bit files, create another XML file (configuration2024-32.xml), change the OfficeClientEdition to 32 and a different folder for the download:
<Add OfficeClientEdition="32" Channel="PerpetualVL2024" SourcePath="C:\Office2024\32\"> <Product ID="ProPlus2024Volume">
Note, there is a 3-line section for Visio that can be deleted if you don’t need that:
<Product ID="VisioProRetail"> <Language ID="en-us" /> </Product>
Perform the Download
Open the Command Prompt window and run this command, or better yet, create a BAT file in the ODT folder which can be used to download both setup files like this:
setup.exe /download configuration2024-64.xml setup.exe /download configuration2024-32.xml
Each version is about 2.5 GB and includes many files, so it will take several minutes for the files to download depending on your connection speed.


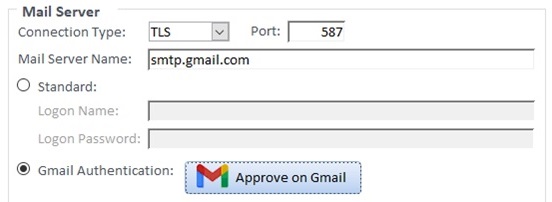
 Google sends emails with its SMTP server at smtp.gmail.com. A few years ago, to increase security, Google required users to explicitly set Gmail accounts to allow Less Secure Apps for this feature.
Google sends emails with its SMTP server at smtp.gmail.com. A few years ago, to increase security, Google required users to explicitly set Gmail accounts to allow Less Secure Apps for this feature.